Updated PSA : Wasabi Wallet is the target of ongoing behavior that appears to be a Sybil Attack since January 2019
PSA
— Samourai Wallet (@SamouraiWallet) July 22, 2019
There exists an entity operating as a de-anonymizing “hot wallet” present within transactions by Wasabi since June 1, 2019. This entity has been clustered very easily due to flagrant address reuse, and downright bizarre behavior. This impacts ALL users since June.
👇👇
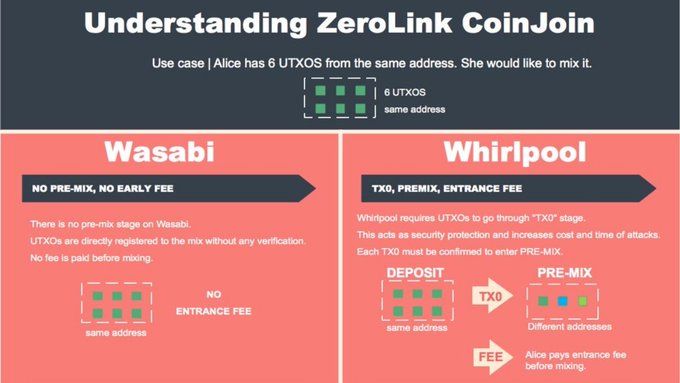
On July 22nd we disclosed that an unknown entity was engaging in a strange pattern of address reuse within Wasabi Wallet transactions created since June 1, 2019. The disclosure focused on a single entity (ANON-2300390908). This entity was easy to discover due to very uncommon behavior, such as using the same address on both sides of a mix transaction. Our claim was that this behavior could indicate an attempt to de-anonymize users of the platform as well as highlighting an incomplete implementation of the ZeroLink protocol as coded by Wasabi Wallet.
Our continued investigations have revealed systematic and ongoing patterns of behavior resembling a Sybil attack within the Wasabi platform. There are a small number of entities (perhaps a small group of users, or a single user) that represent a large part of the UTXOs active in Wasabi mix transactions. This activity has been ongoing in various waves of intensity since January 2019.
This report will show:
- The ANON-2300390908 is likely using a custom client that leaves behind an address reuse fingerprint since at least June 2019 that significantly degrades the anonymity set above and beyond what Wasabi is willing to account for.
- The same patterns of behavior seen in ANON-2300390908 can also be seen in other entities with increasing levels of intensity and frequency starting January 2019 and repeating May 2019.
- Address reuse is a far more common event than initially disclosed by us or acknowledged by the Wasabi team, and is not limited to the initial dates or the entity we previously disclosed.
- An unknown actor is engaging in behavior that resembles a Sybil attack against the coordinator by progressively gaining a larger share of the total UTXOs active in the mixer.
Based on the presented factual data this report will offer a hypothesis to attempt to explain this behavior, as well as pose formal questions to the operators of Wasabi Wallet.
Wasabi Wallet response to initial disclosure
The only official response to the July 22nd disclosure came from Wasabi Wallet CTO nopara73 in a post on Reddit.

Personal attacks aside — which have no place in any technical argument— we do not believe this response takes the threat of the initial disclosure seriously and misleads users of the platform into a false sense of privacy. Ignoring the second paragraph entirely, and ignoring the overall dismissive tone we ascertain important facts from the following sentence:
“Someone changed two lines in Wasabi codebase to reuse 2 addresses”
We take this as confirmation that this type of behavior is not possible using the official binaries of Wasabi Wallet. We also suspected this entity was using a modified client, as allowing for address reuse would break compliance with the ZeroLink protocol and the Wasabi client allowing for this would be surprising.
“Instead of 100, your anonymity set becomes 99”
We strongly disagree with this statement, and believe that this report will demonstrate the greater impact of that this particular case of address reuse on the overall anonymity set is greater than 100–1, but more more seriously than that, the stated upper bound of the anonymity set of 100 doesn’t give any guarantee to the actual lower bound of the true anonymity set.
Key Takeaway:
- As per Wasabi CTO statement, ANON-2300390908 is likely using a custom client that leaves behind an address reuse fingerprint since at least June 2019
Occurrences of Address Reuse within the Wasabi platform
In order to accurately estimate the impact of address reuse within Wasabi transactions we first needed to get an overall picture of the situation. As all the data is freely available on the public blockchain, we analyzed 4,504 Wasabi mix transaction up until July 23, 2019. We found even more surprising results than we expected. The raw numbers give the first clue that address reuse is a far more systemic problem than we initially thought.
Total number of transactions:
4,504
Number of unique addresses:
502,305
Number of occurrences of address reuse:
19,957
Number of unique addresses clustered into an address reusing entity:
30,052
A lower bound estimate of ~6% of the addresses within the Wasabi platform are controlled by the entities that create these clusters. We can assume that many of these entities are using the same custom client that creates the same address reuse bug previously described.
Ignoring the fact that a fully implemented ZeroLink protocol would not allow for any address reuse, we can see this is a larger and longer running issue than just a single user running a modified client since June.
The following chart displays the number of address reuse occurrences per day.

From October to early January we see very minimal occurrences of address reuse. Again, we will ignore the fact that the coordinator should not allow these transactions to be broadcast at all and say during this period address reuse is in the “normal” range. We can attribute these cases to a few users running multiple clients at the same time and other hiccups.
Key Takeaways:
- ~ 6% of all addresses in all Wasabi transactions are clustered into entities who create the same address reuse fingerprint as the entity ANON-2300390908 — meaning 6% of all addresses are presumably controlled by one or more entities using the same custom client.
- Prior to mid January 2019 levels of address reuse could be considered “normal”. Some event occurred in January that changed this, and created a “new normal”
The Consolidation Problem
Wasabi users are more likely to consolidate their mixed UTXOs into a transaction that creates a single deterministic link because there is currently no Postmix spending strategies employed to mitigate and protect against common patterns of user behavior — such as indiscriminate consolidation.
Consolidation imparts a negative privacy consequence for all peers involved in mix transactions with the consolidating entities.

The existence of entities who are exhibiting patterns of behavior consistent with a Sybil attack — which will be explored in the next section — in combination with the unusually large number of addresses reused in the platform, and the common and frequent clustering of legitimate users presents serious challenges when attempting to gauge the true effectiveness of the privacy gains in a given mix and the impact on the true anonymity set.
Let us review a flagrant example of consolidation, these two transactions contributed heavily to the formation of the original ANON-2300390908 cluster.
- 3c8c1b6329bebe71299f4452c9d75322ff775f9528c1847cd1110ca68fc9d26d
- 58bc988519e719e714cc763561dcda93392a9e47496757be47881c3bf7a1a26a
Key Takeaways:
- Legitimate users that spend more than one mixed UTXO at a time are likely to be impacted by clustering due to lack of any provided Postmix spending tools.
- Entities using the modified client also aggressively consolidate UTXOs.
- The address reuse bug in combination with aggressive consolidation led to the eventual clustering of ANON-2300390908.
Three Distinct Waves
The chart plotting occurrences of address reuse per day makes it obvious that there was an explosion of daily address reuse within the Wasabi platform from around January 15, 2019. Most interestingly we can see the formation of three distinct waves of reuse occurrences.

An important clue that may fit into the timeline is the major release of Wasabi version 1.1 around the time of the start of first wave in mid January. This update introduced a new algorithm that allows for multiple mix denominations. This fact, while not conclusive, may suggest that the increases in the number of occurrences may be related to a small number of “users” entering the platform with a large amount of BTC.
[RELEASE] From now on Wasabi can mix large amounts faster by mixing on the change. Big thank you for eveyone who contributed to reach this milestone!https://t.co/JJxgGNi1TD
— nopara73 (@nopara73) January 12, 2019
We can further break down the average number of occurrences of address reuse in mix transactions. Of course, a higher number of reused addresses in mix transactions directly impacts the upper bound anonymity set in the most obvious way, which will be covered as an addendum to this report.
We can observe obvious spikes of address reuse that correspond with the previously defined wave pattern.
Compare the address reuses per transaction with an upper bound estimation of new BTC incoming into the platform. You find there is a direct correlation with the injection of large amounts of BTC and the peaks of address reuse.


From these two charts we learn an interesting clue. Each wave of this activity is preceded by a large amount of unmixed BTC introduced into the platform.
The final chart to observe is the number of UTXOs entering the mixer. This chart suggests a step pattern with the last three steps having their boundaries aligned with the waves observed on the previous charts.


This step pattern and alignment with the previously described waves is a strong indication that an unknown actor is behaving in a way that appears to Sybil attack the Wasabi coordinator by progressively gaining a larger share of the active UTXOs in the platform.
It is important to note that just because the pattern of behavior is indicative of a Sybil attack, we are not attributing maliciousness to this entity. For example, one can theorize this entity might be a “nice whale” who engages in an altruistic activity of padding the transactions with their own UTXOs when the platform lacks the liquidity to mix large (and sudden) influxes of BTC. However, regardless of intent, the behavior is consistent with a Sybil attack.
Key Takeaways:
- There have been three distinct waves of abnormal behavior.
- Each wave begins after a large amount of unmixed BTC is sent to the mixer
- Each wave ends with a “falling wedge” pattern which is best illustrated in Wave 2 completed mid May.
- Wave 3 began mid May and is currently ongoing. This wave includes a larger volume of address reuse than the previous waves.
- Multiple clusters of entities since January all likely using this same modified client, but none of these entities bothered to fix the bug in all that time.
Review
There are primarily three distinct yet intertwined issues highlighted in this report that must be considered together.
- The consolidation of Postmix UTXOs leads to the deterministic clustering of legitimate users. This weakens the privacy provided by the mixing platform when a legitimate user creates transactions that exit the platform. — This can be mitigated with proper coin control techniques if the user is sophisticated and disciplined enough, though mistakes are easy to make and frequent.
- Rampant and explosive occurrences of address reuse occurring in three distinct waves since mid January 2019 has led to the creation of large distinct clusters of entities that share a common address reuse fingerprint, suggesting these entities are all sharing a custom client software — which may indicate these entities are known to each other, or are the same person. These entities also engage in larger than normal consolidation transactions that weaken the anonymity set of the transactions they participated in.
- The revelation of these entities and their observed patterns over the last 6 months — including both address reuse and consolidation behavior — and the correlation to three distinct waves, suggest that an entity is acting in a way that resembles a malicious Sybil attack on the mixer.
Possible Scenarios
As the facts — as recorded in the blockchain — have been presented, we may allow ourselves a moment to think through the motivations and incentives of an actor exhibiting the patterns of behavior that have been observed.
We have shown that actor exhibits certain characteristics:
- Use of a modified client that leaves a distinct fingerprint with Wasabi transactions they participate in due to an address reuse bug.
- An overwhelming tendency to create large consolidation transactions of previously mixed UTXOs and “unmixed change”. These consolidations are sometimes sent off the platform and sometimes re-injected them back into the platform to be mixed again.
- Increased activity directly after the injection of large amounts of BTC into the platform.
With these facts we can imagine three scenarios and attempt to think through them.
Scenario A — Malicious Actor
A malicious actor looking to spy on Wasabi users is attempting to gain an ever larger share of UTXOs within Wasabi mixes. This is a classic Sybil attack that can affect any CoinJoin coordinator. An example of this actor would be a chain analysis firm.
This actor would have surely patched the address reuse bug sometime between January and July, as this bug creates a fingerprint that sticks out from the crowd and would be noticed sooner rather than later. This actor would have an interest in not being noticed and would have the means to correct the bug easily. If the actor is a chain analysis firm they would be well placed to detect the footprints and quickly correct them.
Given the information that we have available this scenario is the least likely.
Scenario B — Honest Actor
An honest actor with a large amount of BTC to mix is running a custom client(s) in order to speed up the mixing process. This custom client contains the address reuse bug.
This honest actor would have surely noticed heavy reuse sometime between January and July and since this actor has an interest in legitimately mixing their BTC would have taken appropriate steps to gain the privacy advantage they originally sought from the service. Additionally, where would this honest actor get this modified client from and why would an honest actor need a modified client?
While still unlikely this scenario is more plausible, especially if the honest actors are also attempting to mix large amounts.
Scenario C — Whale Sidekick
This actor would pad transactions with their UTXOs whenever the mixing platform received a sudden large influx of BTC that it wasn’t sufficiently capable of handing. The Whale Sidekick would utilize their UTXOs using a custom client to provide injections of liquidity resulting in mixing cycles that complete quickly at the expense of a degraded anonymity set. Use of the modified client revealed address reuse by this actor.
What would the incentive be for this actor to provide this seemingly altruistic liquidity service? What interest would this actor have in ensuring other Whales have a fast and liquid experience? Where did the custom client come from? Is this actor aware they are degrading the anonymity set by engaging in this practice?
We believe this scenario to be the most likely, with incentives pointing to a collusion between this actor and the coordinator in an effort to bootstrap liquidity and provide a fast mixing experience. This is not an accusation or a statement of fact, rather it is the scenario that makes the most sense given the information that is known.
Conclusion
While this report isn’t as conclusive as we would like — if anything it has raised more questions than it has answered — but instead of speculating as to the motivations of these actors we will instead focus on the facts revealed in the course of the report. We have shown:
- That a systemic and ongoing address reuse problem within Wasabi mixes has existed since mid January 2019
- There have been three distinct waves of increased address reuse, with the third wave beginning May 2019 and currently ongoing.
- The start of each wave appears to correspond to a large injection of BTC/UTXOs into the platform
- Entities that engage in systematic address reuse also aggressively consolidate their mixed UTXOs which reveal clusters of non reused addresses associated to these entities.
We suspect this is only the beginning of the story. However, we hope that Wasabi takes this report seriously, examines the evidence provided, responds in a professional manner devoid of personal attacks, and takes the lead on responsible and honest communication with their own user base. We believe a response from the Wasabi team is warranted and should include answers to the following questions:
- Is the Wasabi team aware of the observations highlighted in this report (three wave periods of increased address reuse, step pattern, consolidation, etc…)?
- If the Wasabi team is aware, do they have an idea of the cause of this phenomenon? Is there a reason why they didn’t think it was important to disclose this information to users?
- Does the Wasabi team still believe this to be a custom client run by one person or several users?
- Is Wasabi aware of any unofficial clients circulating that would encourage the appearance of increased volume within the mixer?
- Does the Wasabi team intend to complete their ZeroLink implementation to prevent transactions that would compromise user privacy from completing in the first place?
We would like to conclude with a brief note, it has been suggested by the Wasabi team that Samourai is acting in bad faith with these disclosures, and that we are acting to intentionally harm Wasabi Wallet. It has even been suggested that we are staging this address reuse attack on Wasabi ourselves. These allegations couldn’t be further from the truth. We strongly believe that the more privacy tools users have at their fingertips the better, and only wish to see Wasabi improve the service they offer to users. This second disclosure has been published in an attempt to demonstrate to the Wasabi Wallet team that a problem exists. Of course, acknowledging the problem is the first step to understanding and eventually fixing it. We conclude with a final Latin maxim that we hope all can agree on and work towards.
Felix qui potuit rerum cognoscere causas — Happy is he who has been able to understand the causes of things.
Addendum
Examining Impact on Anonymity Set
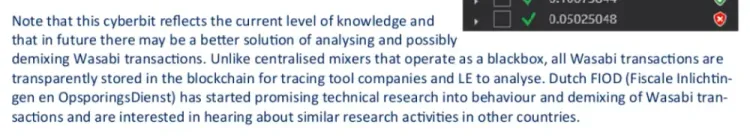
As the Wasabi team has described it, the goal of the Wasabi mixing technique, is to hide your UTXOs in a “sufficiently” large crowd (peers). The size of the crowd is referred to as an Anonymity Set. The current anonymity set calculation relies on an assumption that there is no link between the transactions inputs participating in a mix. The current target Anonymity Set in Wasabi mixing is 100 peers.
In response to the initial disclosure it was repeated by Wasabi CTO that the large number of peers protected honest users from the actions of a single rogue bad actor. This is referred to as the “100–1” argument and is superficially true if you assume that each input is a unique peer.
However, in the case of Wasabi transactions it is dubious and easily dismissed with a critical look at the transactions that are created. The continued use of this simplistic metric of Anonymity Set is damaging to users, as it instills a false sense of privacy and perpetuates a misunderstanding of this metric.
In order to examine the veracity of the “100–1” claim we have developed tools that examine the composition of any transaction, including transactions created by Wasabi. These tools make an effort to record:
- Explicit deterministic links that exist between input and output — These links can be considered to have an anonymity set of 0
- Where UTXOs have been seen together in previous mix transaction (regularly between 40–60%) — These links degrade the anonymity set though just how much is up for debate.
- Deterministic links left behind by the “unmixed change” — These links can be considered to have an anonymity set of 0.
- Outputs that have been consolidated — These links generate clusters that reveal common ownership of outputs in a given transaction, reducing the overall entropy of the transaction.
- Inputs that belong to the same entity — These links can be considered to have an anonymity set of 0.
These listed factors, in addition to the details in this report that a small group of entities have captured a large amount of UTXOs in the mixer, degrade the true Anonymity Set from the stated 100 peers significantly.

As a public service we have made these tools available freely to the public so that they may responsibly audit and inspect transactions and ultimately come to their own conclusions with the data provided. We hope the public use of these tools encourages a more honest discussion around Anonymity Set in general. Over the coming months we will be investing material resources and engaging in dialogue with the users and experts on the best way to measure and report on this metric going forward.
A knowledgeable and informed user is a more private user. We suggest all users make use of the analysis tools we have created and provide open source to begin auditing their own transactions. We strongly condemn any attempts to discourage users from responsibly inspecting their transactions.


Member discussion